题目
Practical CTF Strategies (112025-MHH) Mini CTF Lab Challenges Series - Computer Forensic
单项选择题
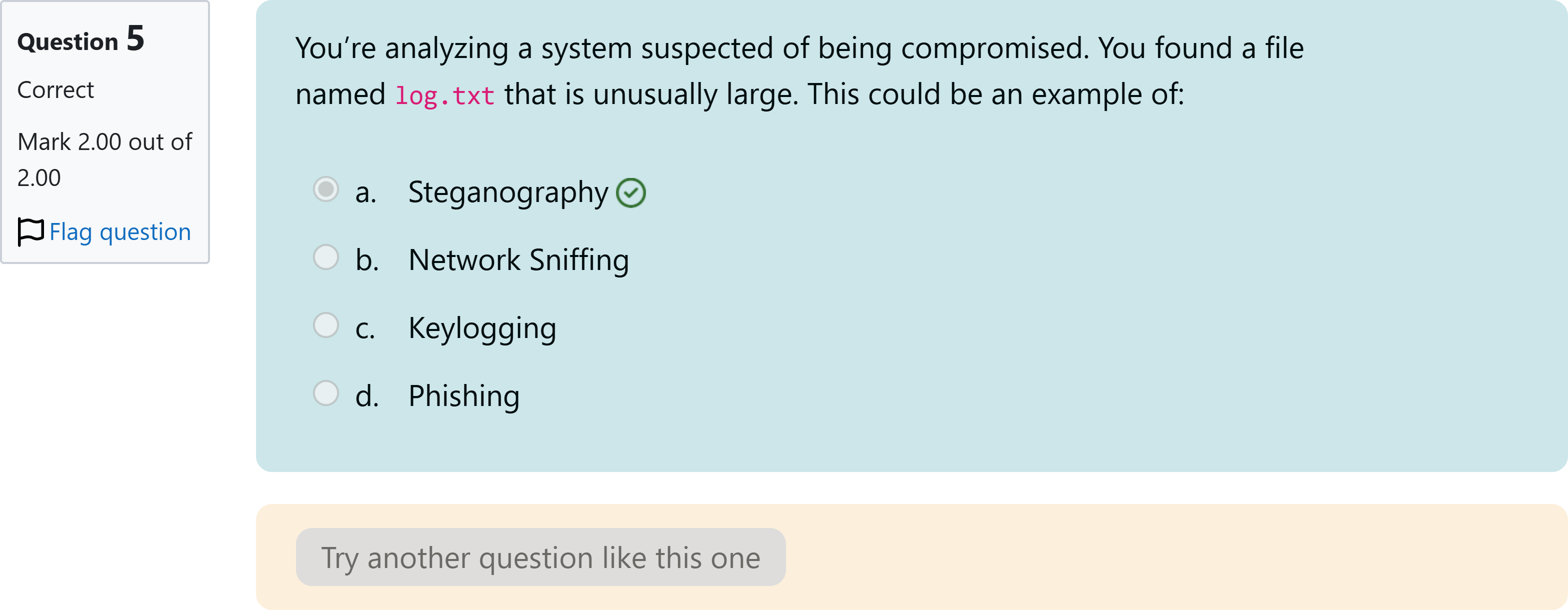
You’re analyzing a system suspected of being compromised. You found a file named log.txt that is unusually large. This could be an example of:
选项
A.a. Steganography
B.b. Network Sniffing
C.c. Keylogging
D.d. Phishing
查看解析
标准答案
Please login to view
思路分析
When evaluating what an unusually large log.txt file could indicate, we should consider what each option implies about system activity.
Option a: Steganography. This technique hides secret information within other non-secret data (like images or audio). A large log file does not inherently indicate hidden data within media; steganography is more about covert data embedding than generating voluminous log files. Thi......Login to view full explanation登录即可查看完整答案
我们收录了全球超50000道考试原题与详细解析,现在登录,立即获得答案。
类似问题
Water on MarsYou join a team of astronaut, landed on this beautiful red planet and manage to capture an image of that planet. Once you come back to earth, you look again into the picture, something seems weird with the picture. Find it and wrap it in apuCTF{flag}Flag format: apuCTF{flag}
You’ve just received a suspicious image file that may contain hidden data. Which of the following tools would you use to analyze it?
You’ve been given a task to hide a secret message within a video file. Which of the following tools would you use?
In a consumer society, many adults channel creativity into buying things
更多留学生实用工具
希望你的学习变得更简单
加入我们,立即解锁 海量真题 与 独家解析,让复习快人一步!