题目
Introduction to Security and Forensic Technologies (CT046-3-1-ISFT-25-RESIT)
单项选择题
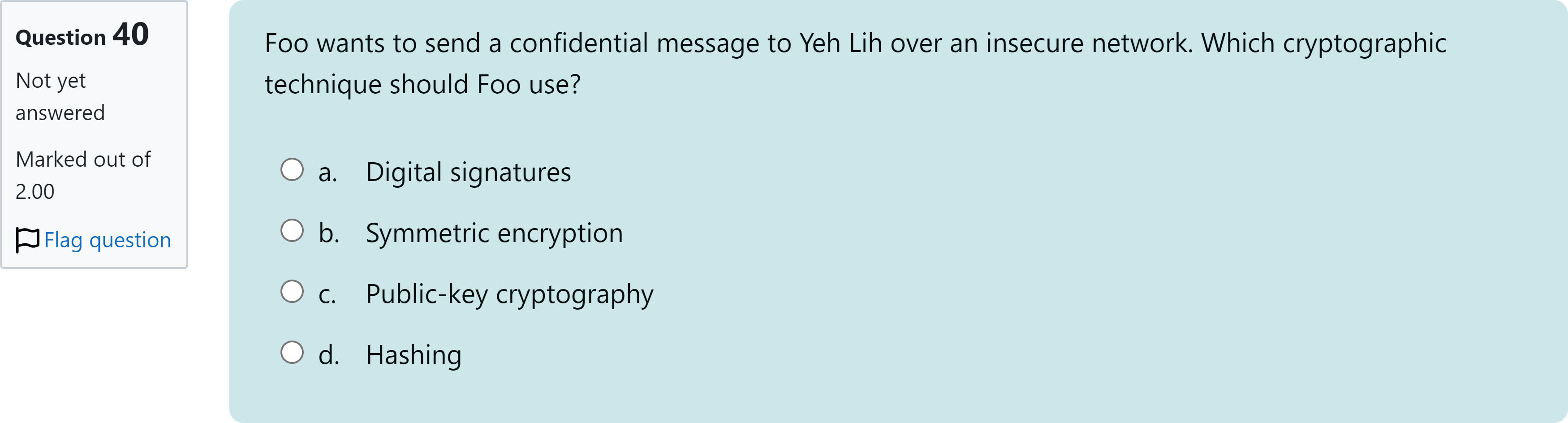
Foo wants to send a confidential message to Yeh Lih over an insecure network. Which cryptographic technique should Foo use?
选项
A.a. Digital signatures
B.b. Symmetric encryption
C.c. Public-key cryptography
D.d. Hashing
查看解析
标准答案
Please login to view
思路分析
When evaluating how Foo should send a confidential message over an insecure network, it helps to think about what each technique actually provides.
Option a: Digital signatures. These are primarily about authenticity and integrity, proving who sent the message and that it hasn’t been alte......Login to view full explanation登录即可查看完整答案
我们收录了全球超50000道考试原题与详细解析,现在登录,立即获得答案。
类似问题
Which cryptographic algorithm is widely used in PKI encryption?
Blank ______ key encryption uses two keys: a public key that everyone can have and a private key for only the recipient.
(CISA exam, adapted) To ensure confidentiality in an asymmetric-key encryption system, knowledge of which of the following keys is required to decrypt the received message?
Suppose Alice encrypted a message using Bob's public key and sent it to Bob. If an attacker was able to intercept Alice-Bob message, which of the following can be compromised:
更多留学生实用工具
希望你的学习变得更简单
加入我们,立即解锁 海量真题 与 独家解析,让复习快人一步!