Questions
Practical CTF Strategies (112025-MHH) Mini CTF Lab Challenges Series - Computer Forensic
Single choice
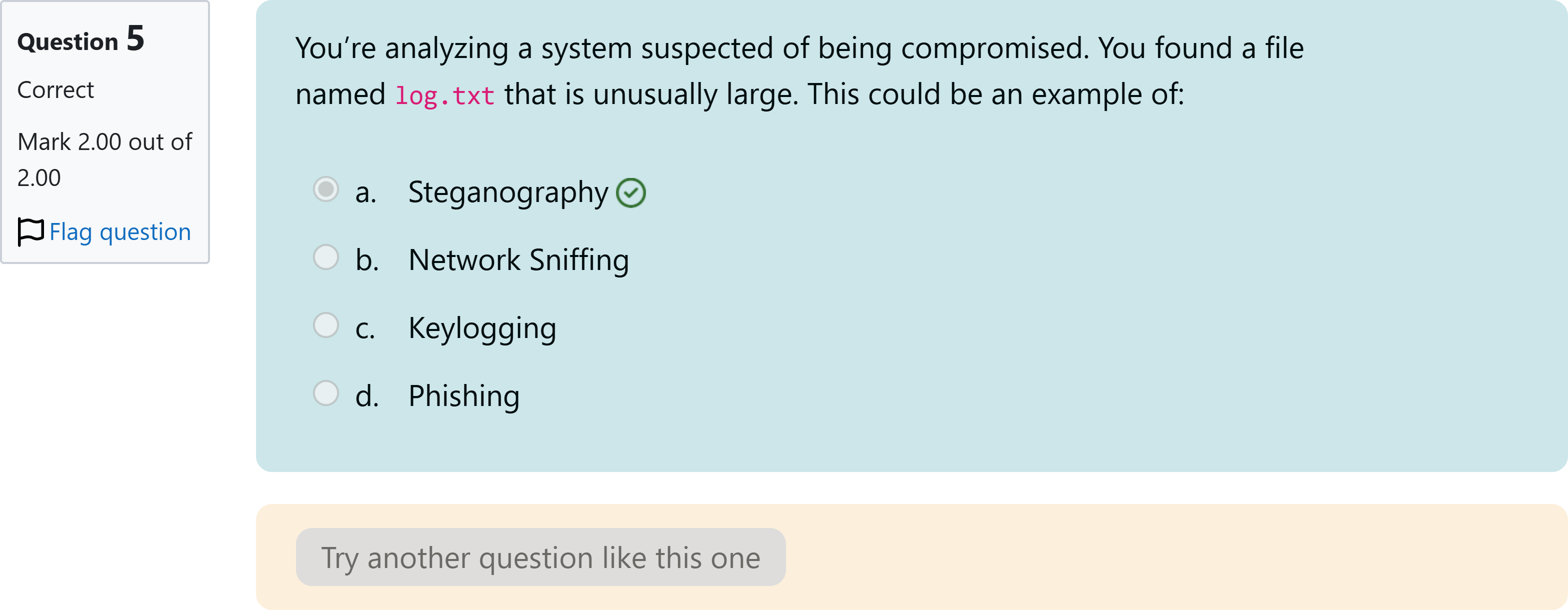
You’re analyzing a system suspected of being compromised. You found a file named log.txt that is unusually large. This could be an example of:
Options
A.a. Steganography
B.b. Network Sniffing
C.c. Keylogging
D.d. Phishing
View Explanation
Verified Answer
Please login to view
Step-by-Step Analysis
When evaluating what an unusually large log.txt file could indicate, we should consider what each option implies about system activity.
Option a: Steganography. This technique hides secret information within other non-secret data (like images or audio). A large log file does not inherently indicate hidden data within media; steganography is more about covert data embedding than generating voluminous log files. Thi......Login to view full explanationLog in for full answers
We've collected over 50,000 authentic exam questions and detailed explanations from around the globe. Log in now and get instant access to the answers!
Similar Questions
Water on MarsYou join a team of astronaut, landed on this beautiful red planet and manage to capture an image of that planet. Once you come back to earth, you look again into the picture, something seems weird with the picture. Find it and wrap it in apuCTF{flag}Flag format: apuCTF{flag}
You’ve just received a suspicious image file that may contain hidden data. Which of the following tools would you use to analyze it?
You’ve been given a task to hide a secret message within a video file. Which of the following tools would you use?
In a consumer society, many adults channel creativity into buying things
More Practical Tools for Students Powered by AI Study Helper
Making Your Study Simpler
Join us and instantly unlock extensive past papers & exclusive solutions to get a head start on your studies!