Questions
Single choice
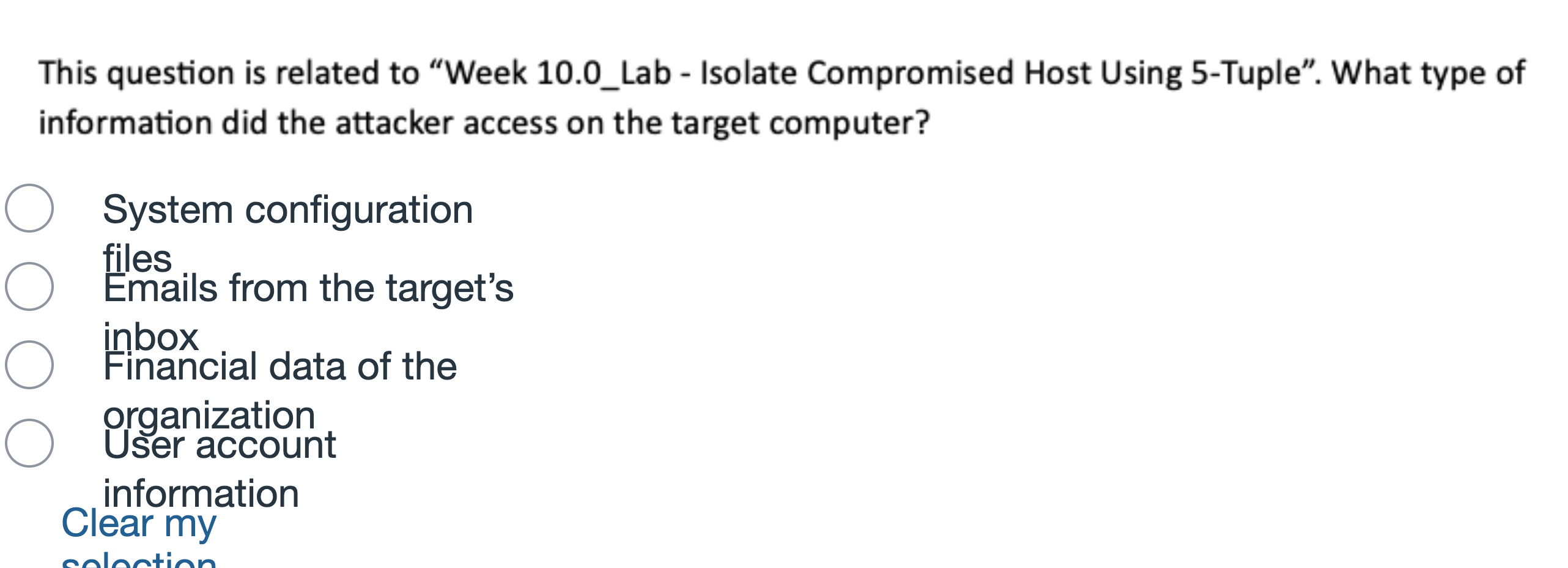
Question at position 23 System configuration filesEmails from the target’s inboxFinancial data of the organizationUser account informationClear my selection
Options
A.System configuration files
B.Emails from the target’s inbox
C.Financial data of the organization
D.User account information
View Explanation
Verified Answer
Please login to view
Step-by-Step Analysis
The question presents four possible data types and asks which one reflects the information accessed on the target computer.
Option 1: System configuration files. This would indicate access to settings and configuration details of the system itself (like OS, startup scripts, or service configurations). While those files are sensitive for system administration, they do not describe the ......Login to view full explanationLog in for full answers
We've collected over 50,000 authentic exam questions and detailed explanations from around the globe. Log in now and get instant access to the answers!
Similar Questions
During incident containment, which action is correct?
Question at position 19 When the attack is minor and unlikely to escalateWhen the root cause of the incident has been identified and requires extensive remediationWhen an organization has unlimited resourcesWhen there is a lack of skilled personnel to manage the incident
Question at position 17 NIST Special Publication 800-61r1 NIST Special Publication 800-61r2 NIST Special Publication (SP) 800-53NIST Special Publication 800-86
Question at position 13 What protocols/software/policies/hardware is in place to prevent this incident from reoccurring?What happened, and at what time?What indicators of the incident might the organisation detect?Were any wrong actions taken that caused damage or inhibited recovery?What precursors of the incident, if any, might the organisation detect? Would any precursors cause the organisation to take action before the incident occurred?What information was needed sooner?Is a policy established to classify it as a malicious activity? If so, then what part of the policy is violated?How well did the incident response team deal with the incident? Were processes followed, and were they sufficient?
More Practical Tools for Students Powered by AI Study Helper
Making Your Study Simpler
Join us and instantly unlock extensive past papers & exclusive solutions to get a head start on your studies!